Since Single Sign-On was completely rebuilt from the ground up in vSphere 5.5 I was in a bit of a struggle while configuring roles and permissions for users accessing VMware vCenter.
With Single Sign-On (from here simply referred as SSO) redesign in vSphere 5.5 VMware introduced a new common domain named vsphere.local.
Users
authentication is now managed by SSO server and not by vCenter itself.
This is because VMware is looking to provide a common authentication
platform across all its services. SSO now lets users authenticate into
vCenter, vCD and vCO. New products, like vCOps, will probably
authenticate users against SSO in their future releases.
So, here's how to create users, groups and manage permissions in vSphere 5.5.
First login to vSphere 5.5 Web Client which, by default, is accessible from this URL:
https://<your_vCenter_Server_IP_or_FQDN>:9443/vsphere-client
Login into vCenter with following credentials:
User: Administrator@vsphere.local
Password: vmware
NOTE: This is the default password for VMware vCenter Server Appliance. If you deployed vCenter as standalone installation you were prompted to choose for a password during installation process.
Go to Roles -> Single Sign-On -> Users and Groups. Click the green New User button to add new users.
Ensure that vsphere.local is set in Domain picker. This is because our users will not be local users but will be authenticated against SSO server.
Now let's create a Group. Move to Groups tab and click New Group button.
Then to add user(s) to this group select the newly created group, click Add Member icon, select user(s), click Add, then Ok.
Finally we need to assign our user(s) or group(s) permissions within our specific product. In this case we assign permissions within vCenter. Permissions are assigned product-wide and not domain-wide this is because a certain user or group could for example retain administrative permissions in vCenter and read-only permissions in vCD.
Go to your vCenter, click Manage -> Permission tab, add button
Click Add, select VSPHERE.LOCAL in Domain picker, choose your group, or user if want to grant permission only to single user and not to entire group, then click Add -> Ok.
Select role for user/group then click Ok.
You can now login with new user's credentials to verify correct permission grant.
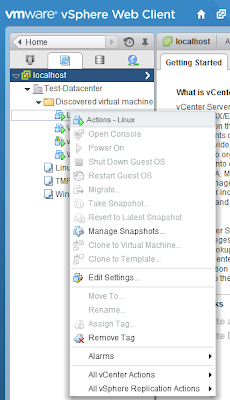
Since in this example TestUser is member of TestGroup which has Read-Only permission assigned we can access vCenter and its object but cannot manage/interact with them as expected.
Permissions can be customized to properly fit your specifications. This can be done by accessing Roles -> Access Control -> Roles.
There are two different groups of roles: system roles, which cannot be modified, and sample roles that can be edited.
If you need to create a custom role best practices suggest you to clone an existing one and edit the cloned one.
That's all!!








Hi, this was a very clear and helpful post on setting up users, groups and roles in vSphere 5.5! Just what I was looking for - grazie!
RispondiEliminaGreat document. This is what I was looking for
RispondiEliminaThe information given in this article is really informative and amazing.
RispondiEliminaHow to assign a machine to a user in VMware